Preventing Theft of Email Passwords and Credit Card Numbers when Using Public Computers I remember sitting in a bar in Honduras with some tall blond girls from the Netherlands. They were very confused. Their credit card security had been compromised at some point during their trip through Central America, even though they were still in [...]
Preventing Theft of Email Passwords and Credit Card Numbers when Using Public Computers
I remember sitting in a bar in Honduras with some tall blond girls from the Netherlands. They were very confused. Their credit card security had been compromised at some point during their trip through Central America, even though they were still in possession of the cards themselves.

Credit card security when traveling
“We think maybe the guy at the hostel opened the locks on our bags and copied the numbers,” one of them told me.
I had other guesses as to what happened: “Did you buy anything online from a public computer recently?”
They had purchased plane tickets, but did not quite comprehend what this had to do with anything.
“But nobody could see our card.”
“They don’t have to.”
This morning I received an email from an old friend named Josh. The email’s subject heading was “VACATION PROBLEMS . . . JOSH.” The body of the email went as follows:
I am writing this with tears in my eyes… My family and I came down here to United Kingdom for a short vacation,unfortunately we got Robbed at the park of the hotel where we stayed. All cash, credit cards and cell were stolen off us but luckily for us we still have our passports with us.
We’ve been to the embassy and the Police here but they’re not helping issues at all and our flight leaves in less than 3hrs from now but we’re having problems settling the hotel bills and the hotel manager won’t let us leave until we settle the bills.
Am freaked out at the moment…
Josh
I read this email and said no way. My friend Josh travels, and he very well may be in the UK with his family, but he did not write this email. The tone, content, and the lack of prospective solutions were not his own. My friend Josh may very well sprout tears from his eyes from time to time, but there is no way that he would be so wussy as to tell me about it. Josh’s email account had been hacked.
The message that was sent out to his contact list was to requisite some heroes to step up and quickly send over money so that “Josh” could settle his hotel bill and get out of the UK. I like how the conductor of this scam made the situation seem urgent by saying that his flight was leaving in 3 hours, giving the impression that money is needed immediately in order to rush people to send over money before checking the facts. I am also impressed by how this email did not directly solicit funds, but rather was sent out as a query letter — a hook — to draw any potential sucker into a funnel of confidence through which they would quickly lose their money trying to help out their old friend “Josh.” The con artist had, apparently, done this before.
This type of email account hacking is becoming common, and this was not the first email like it that I had received from a friend’s compromised email account.
How email account and credit card security can become compromised
What is happening here? How could the girls from the Netherlands have their credit card numbers swiped without ever loosing contact with their cards? How could Josh have his email account compromised?
There are many ways both of these actions could have been perpetrated, but one is so simple that any fool who can upload a program to a computer can execute with brash efficiency:
Keylogger programs.
As I explained to the Netherlands girls, “There are programs that can be uploaded on a computer that record keystrokes, so when you enter your credit card number into the web page these programs can pick it up and make it available to anyone who wants it.”
These programs record all keystrokes entered into a computer, including bank account numbers, email passwords, Facebook account info. The execution of this theft is so incredibly simple and that the potential for it becoming widespread is high. Just about anybody can use these programs: all they need to do is download it, upload it onto a computer that other people may use to make online purchases, comeback throughout the day and seize the spoils. The companies who make these programs justify themselves by saying that they are meant to be used as a way to backup data that you enter into your own computer, but, as is obvious, this is not really how they are used.
NEVER ENTER SENSITIVE INFORMATION INTO A PUBLIC COMPUTER.
Sensitive information means passwords, bank account log info, or credit card numbers. Entering this information into a public computer may mean giving it away to anyone who may want it.
I published this advice years ago, but knowledge of this scam still is not widely known. I become severely annoyed when my wife uses a public computer to check her email, I become enraged to see other travelers entering in their credit card info on a public computer.
Are you trying to be robbed?
Any keystroke entered into a computer that multiple people use can be easily recorded and used by unauthorized parties. If you don’t trust showing your credit card to someone then don’t put its numbers into a public computer.
It will probably always be unclear if it was a keylogger program that got the girls from the Netherlands or my friend Josh, but it very well could have been.
Keylogger program solutions
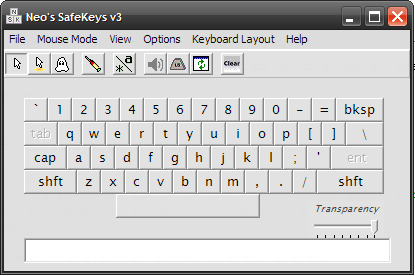
A simple solution to subvert the potential threat of programs that can record keystrokes entered into a public computer has just been made known to me by Andy Hobotraveler.com at Log in safely in internet cafe. The solution is a program called Safekeys v3, which allows a virtual keypad to be called up onto a computer screen when the user wants to enter in private information. This virtual keypad is clicked with a mouse so no data is entered through the keyboard. This programs also claims to offer security against screenlogger programs, which scrap data entered into a computer at screen level.
The Safekeys v3 program also has a portable version which can be run on a flash drive.
Travel tip: never enter sensitive information into a public computer or use a program which offers protection against keylogger and other info scrapping programs.
SUPPORT
The only way I can continue my travels and publishing this blog is by generous contributions from readers. If you can, please subscribe for just $5 per month:NEWSLETTER
About the Author: VBJ
I am the founder and editor of Vagabond Journey. I’ve been traveling the world since 1999, through 91 countries. I am the author of the book, Ghost Cities of China and have written for The Guardian, Forbes, Bloomberg, The Diplomat, the South China Morning Post, and other publications. VBJ has written 3715 posts on Vagabond Journey. Contact the author.
VBJ is currently in: New York City
-
March 22, 2011, 2:23 pm
LinkHoly geez! This is great! I like the knowledge. I really worry about this stuff and I hope I don’t ever have to deal with it. I am now confirmed that I’ll be traveling with my own netbook.
Thanks!
-
March 22, 2011, 7:10 pm
LinkCheck out travelvice craigs site he had something about you can browse from firefox installed on a USB drive that will prevent keylogging
-
March 23, 2011, 1:30 am
Linkthat safe keys program is easily logged as well if someone wanted to. If its plugged in it can be tapped.
-
March 23, 2011, 1:17 pm
LinkABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789
abcdefghijklmnopqrstuvwxyzThen cut and past. This works with your user name as well, assuming the stealer program does not use image capture. You can also just type your password out of order by clicking in different possitions as in as then click before the as and type p, then click at the end and type ord, then click where the w should to and type sw and you have “password” throw in some random letters/numbers in places and delete these at some point. This gives a scrambled stream of keystrokes not resempling your password at all. I ahve used this on computers that for some reason I could not run “safe key” on.
But no matter what you do, you are never 100% safe on the internet. You can only take as many precautions as reasonable. Sometimes it is best to walk right past a “free” computer in your hostel/hotel. These can be seriously buggy. Better to go down the street to a site that “apears” to be safer and more popular. Again, no guaruntees.
Bob L
-
March 26, 2011, 2:55 am
Linki have a firewall up for microsoft, but because i have so many protections, i don’t know which firewall i should be using. i have norton, pc tools, malwarebytes, xoftspyXE and McAfee. none of these things are worth a dime.i have trackers, trojans, remote hackers, etc. i have had the most complete episode of identity theft ever with my total computer file info displayed on the internet. if these security systems are all wrong, which ones should i be using?
-
October 5, 2011, 2:21 pm
LinkHere’s what I’ve been doing:
First I clean the computer as much as possible with portable versions of Spybot SD and an anti-virus. Second I use the LastPass plugin on a clean install of Firefox Portable. LastPass bypasses keyloggers since you don’t need to enter any information via the keyboard except for your e-mail address and master password. After that it’ll automatically log you in to the websites you visit and can fill out credit card forms etc.
Even then, I still don’t use the keyboard to enter my master-password, but instead use Neo’s SafeKeys to drag and drop. If I really don’t trust the computer I’m using I’ll instead use a list of one-use passwords randomly generated by LastPass and printed out on a piece of paper kept in my wallet. Even if someone manages to get my master/one-use passwords, in order to access all my stored passwords they still have to enter 3 random letters/numbers from the security grid printed out on another piece of paper kept in my wallet. I print out a completely different grid every so often.
If I’m being super-paranoid I’ll try to reboot into Ubuntu from another USB drive or a CD. Though if the BIOS are password protected this won’t work.
It shocks me sometimes seeing the information that people will put into public computers without a thought. The computers in a hostel in Budapest were absolutely riddled with viruses and malware yet even when I told people about this they didn’t really care.
Next post: Staying in Hostels with a Baby
Previous post: How to Learn Foreign Languages